How We Help: Our Service Offerings
Covering emerging and traditional technologies, we consult, deploy and integrate complex IT services across managed network, cloud, security and digital workplace:

Consult and Assess
Design and Implement
Run, Monitor and Manage
Related Posts
Consult and Assess
Design and Implement
Run, Monitor and Manage
Related Posts
Consult and Assess
Design and Implement
Run, Monitor and Manage
Related Posts
Consult and Assess
Design and Implement
Run, Monitor and Manage
Our mission is to be the world’s most trusted technology services partner – inspiring, empowering and enabling the innovation and transformation of today and tomorrow.
Systal has been included as the only new entrant of 17 businesses in the Gartner® 2023 Magic Quadrant™ for Managed Network Services (MNS).
Committed to creating a sustainable global future, Systal aims to be a climate neutral business by 2030.
Systal's certified specialists provide tailored services based on unique customer needs, and built upon strategic counsel and best-in-class technical capability.
Systal's culture is founded upon high-performing people who push themselves, their colleagues and our customers to new heights



















Covering emerging and traditional technologies, we consult, deploy and integrate complex IT services across managed network, cloud, security and digital workplace:
Across our 24/7 Global NOCs, we deliver long-term network transformation and managed services to the world’s largest and most complex enterprises.
Supporting customers across all aspects of their Cloud journey, our experts consult, implement, and bring enterprise Cloud strategies to life.
Our physical and cyber security solutions help enterprise businesses identify, protect, detect, respond, and recover from critical cyber-attacks.
Our consultative, project and managed support services empower enterprises to deliver seamless digital workplace and AI services.
We help businesses achieve strategic technology transformation, minimising the totality of their end-to-end business risk and maximising the business value of their IT infrastructure.


Improve business resilience, meet regulatory compliance and protect enterprise reputation and revenue.
Achieve business growth and agility goals including accessing new markets, facilitating M&A, product diversification and business future proofing.
Improve cost effectiveness by collaborating to maximise your technology investment.
Enterprise Customers
Customer Sites in 93 Countries
Assets Monitored
WAN and LAN Endpoints
Across our global 24/7 Network and Security Operations Centres, we help hundreds of enterprise businesses across multiple industries meet their complex and unique technology requirements.
Case Studies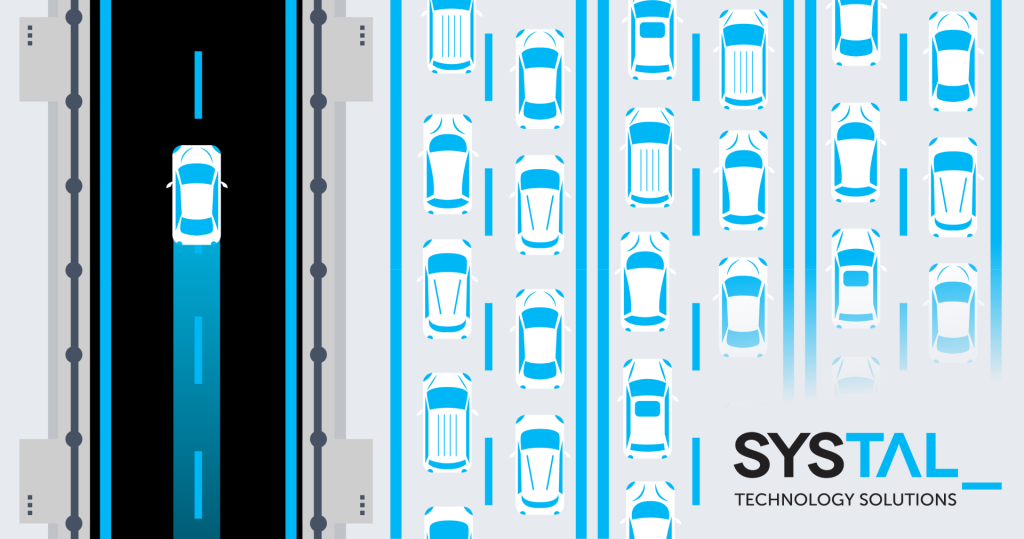
This article explains how out-of-band networks provide a vital service in maintaining business continuity and protecting customer reputation.
Have a question or want to discuss your technology and key business challenges? Arrange an initial consultation with one of our experts.